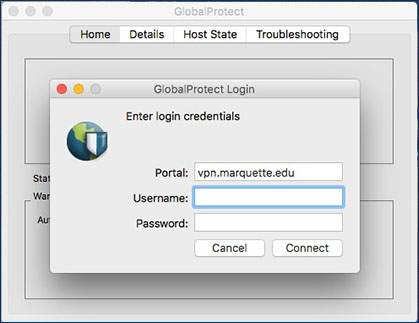
GlobalProtect for iOS connects to a GlobalProtect gateway on a Palo Alto Networks next-generation firewall to allow mobile users to benefit from enterprise security protection. Enterprise administrator can configure the same app to connect in either Always-On VPN, Remote Access VPN or Per App VPN mode. These two documents provide customizable step-by-step procedures for downloading, installing, and using the GlobalProtect app. Separate documents exist for Mac users and Windows users. Each document—written in Microsoft Word for easy editing—highlights areas of the document you may want to customize for your end users depending on your. MAC GLOBAL PROTECT OPERATION. Launch the GlobalProtect app by clicking the GP icon (top right corner of the task bar). The panel will open. Set the portal address to ouvpn.ou.edu and select Connect. Once the GlobalProtect client connects to the portal it will prompt for your username and password.

Resolution
Common Issue 1
Users can start the GlobalProtect portal login, but nothing else happens.
Troubleshooting
- On occasion the GlobalProtect client/Agent may need to be downloaded onto the device again after ensuring all the previous instances have been removed.
- Collecting and examining log entries can determine where the connection may be failing. From these logs it is possible to tell if authentication worked as intended, or if the authentication settings need to be adjusted. It is recommended to gather logs from the GlobalProtect client to see at which stage the error occurred. Logs can be collected under : Troubleshooting > Logs > Log = PanGP Service and Debug level = Debug
- On the firewall, tailing the following logs is needed when an attempt is made from the GlobalProtect user:
- tail follow yes web-server-log sslvpn-access.log
- tail follow yes mp-log authd.log
- Execute the following command to check for current users:
> show global-protect-gateway current-user
Common Issue 2

Resolution
Common Issue 1
Users can start the GlobalProtect portal login, but nothing else happens.
Troubleshooting
- On occasion the GlobalProtect client/Agent may need to be downloaded onto the device again after ensuring all the previous instances have been removed.
- Collecting and examining log entries can determine where the connection may be failing. From these logs it is possible to tell if authentication worked as intended, or if the authentication settings need to be adjusted. It is recommended to gather logs from the GlobalProtect client to see at which stage the error occurred. Logs can be collected under : Troubleshooting > Logs > Log = PanGP Service and Debug level = Debug
- On the firewall, tailing the following logs is needed when an attempt is made from the GlobalProtect user:
- tail follow yes web-server-log sslvpn-access.log
- tail follow yes mp-log authd.log
- Execute the following command to check for current users:
> show global-protect-gateway current-user
Common Issue 2
Authentication works for GlobalProtect Portal but fails on GlobalProtect Gateway.
Troubleshooting
Globalprotect Client Mac
- At the time of authentication on the portal, user credentials are passed from the portal to the gateway. If both the portal and the gateway are configured with the same authentication method, this problem will not occur.
- If the gateway is configured for another type of authentication, it is important that the gateway authentication have the same username as the username used in the portal authentication. If credentials passed from the portal to the gateway are not recognized by the gateway, the user will be prompted to enter the password again.
Important! It is not possible to provide another username, so it is important to have the same username in the two authentication methods. - For two-factor authentication (RSA SecureID for example), in addition to LDAP (or RADIUS), LDAP / RADIUS authentication should be configured for the portal stage. Users will first be prompted to login with their domain username and password, then challenged again (by the gateway) to enter the one-time use password displayed on the RSA secure ID. Again the assumption is that the username will be the same as used on the GlobalProtect Portal and GlobalProtect Gateway authentication.

